How to Hack a Person with Their Phone Number?

How to hack a person with their phone number? Number hacking or phone hacking with a phone number are expressions that we usually hear a lot and we have also seen some people who are looking for a way to hack other people’s mobile numbers.
you probably do not know many of them or even you are not familiar with the exact concept of hacking and phone hacking. In this article, we are going to fully examine the meaning of the term phone hacking and then see how to hack a number or hack a phone with a number. The title of the best applications for spying, eavesdropping, and controlling Mobile phones.
Understanding the hacking Fundamental
According to some experts, the phenomenon of hacking or unauthorized penetration existed before the advent of computers and is not only related to intelligent systems. These experts equate any type of unauthorized access to private and classified information with hacking. they know Anyway, after the appearance of the first computers, hacking has taken a new form.
Today, hacking means the penetration of a person into a computer system without permission to access it. A hacker is someone who can break into your system and do such an act.
The term hacking is not only specific to computers and is also used by people who have a lot of expertise in fields such as music, painting, etc., which means intelligent and creative transformations of a person in that field.
The mobile phone is also a complex issue and we cannot talk about it in this simple way because it is a very general concept if we really mean it correctly, it means that we can completely control and influence other people’s phones.
How to hack phones remotely?
There are many ways to control the phone remotely. But the easiest way to hack the phone of the person you want is to access that person’s phone and install the hacking program on that phone.
Due to the low complexity of this method and the need to learn programming knowledge, we say that it is the easiest solution to control the phone without people’s permission. But if we want to hack the cell phone of a child or family member or other persons without accessing their phone, we must say that this depends on your knowledge in the field of programming and even in the field of installing the number hacking program.
Whether it is possible to hack a phone number or hack a phone at all is a question that arises in the minds of many people who intend to do this. In answer to this question, without trying to confuse you, we must say that yes, hacking the phone and hacking the mobile number are both possible, and many people have been involved in this issue, which has led to significant results.

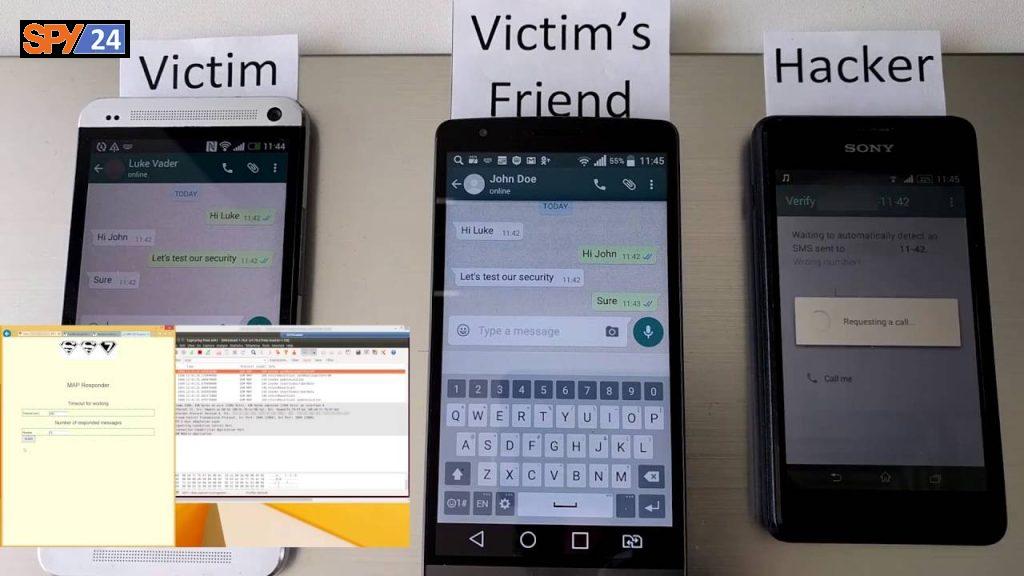
Hacking through the phone number from the exchange network service called Signaling System No. 7-SS7 – uses what is called C7 in the UK and CCSS7 in the US and will act as an intermediary between mobile phone networks.
When making a call or sending text messages on the SS7 network, details such as numbers, message transfers, bill payments, and other actions connect one network or caller to another.
What is Signaling System 7 (SS7)?
Signaling System 7 (SS7) is an international telecommunications protocol standard that defines how network elements in a Public Switched Telephone Network (PSTN) exchange information and control signals. Nodes in the SS7 network are called signaling points.
It is the system that controls how phone calls are routed and billed and enables advanced calling features and short message service (SMS). It may also be called Signaling System No. 7, Signaling System No. 7, or—in the United States—Common Channel Signaling System 7, or CCSS7.
SS7 was first adopted as an international standard in 1988 and the last revision of this standard was done in 1993. This standard is still the current standard for telephone conversations and It is used for landline and mobile phone services up to and including 5G…
By hacking through the SS7 system and using the target person’s phone number, an attacker can track a person’s location through a cell phone, read sent and received messages, listen to and record phone calls, and other information.
Security experts believe that breaking into an unencrypted phone is much easier than we think. To prove this, they have tapped the phone calls of a member of the American Congress.
A German computer engineer named Karsten Nohl believes that hackers will be able to track a person’s place of work, listen to their phone calls, and read their text messages just by knowing their phone number.

Noel managed to track the movements of California Representative Ted Lieu (who had previously agreed to participate in the program) and to record his phone calls by using the phone number and exploiting a known network weakness…
In Mr. Carsten Noll’s method, no action taken by the target person can lead to the disruption of the hacker’s access to the desired information. Any decision that Mr. Ted Liu (the member of Congress in question) makes about pinning the phone, installing and removing a specific application, etc., will not affect the process of hacking the device. The reason for this is actually hacking the device through the communication network!
Unfortunately, at present, more details regarding this matter and the exact method of operation of Mr. Karsten Knoll in order to hack the target phone have not been provided. It is expected that his information will be kept confidential.
Hackers only hack your phone number! What is SS7?
In the following, we want to talk about the security of telecommunication and communication infrastructure services that we are using every day.
Imagine that hackers can observe all your movements and listen to all your phone calls, and they can do this just by having your phone number. Yes, just by having your phone number and without the need to install the smallest software on your mobile phone, and the interesting thing is that you can’t do anything because you are not responsible for establishing this communication system! This is really scary.
Is it really possible? Can they hack us just by having our phone number?
The answer of a German information security expert who has done research on this matter is yes, one of the top information security experts who works at the security research laboratory in Berlin, Germany, says that this is very simple, just by having your phone number. A hacker can gain access to all the conversations and information you exchange through the phone.
Even to prove this, one of the employees of this research center was tested with a simple Apple phone and finally, 60 minutes of this employee’s conversations were recorded and spied on. But one of the top security experts, German Karsten Nohl, who is a member of the hacker team of this security research center, says in this regard that cybercriminals do not actually hack users’ devices in this kind of hacking, but because of the weak security in communication systems and There is a telecommunication infrastructure, they use it, and the user cannot have a share in establishing the security of this mechanism.
This very dangerous security vulnerability is known as Signaling System Seven or SS7, which can virtually hack and spy on almost any phone. As we said, this test was done practically on the volunteer’s mobile phone and after SS7 was used, the phone was officially hacked with only one phone number! After the case was hacked, information such as phone calls, all contacts, text messages, and even GPS information and the location of the target person was visible to the hacker. Although the flow did not end with these things and even the possibility of making contact with the contacts and… was also possible in this hack.
As we said before, this vulnerability is not on your mobile phone and actually exists in telecommunication and telephone infrastructures, installing or preventing the installation of any software on the phone cannot cause a problem in the working process of this vulnerability. in In fact, it is the mobile network that is hacked, not your mobile phone. You will definitely be shocked and angry when you hear this, because your mobile phone may have been spied on without knowing it. In the continuation of his speech, Nohel announced that almost all mobile phones can be hacked with this method.
Regardless of what brand you use. A hacker can use this method to hack your bank accounts, e-mail accounts, etc. because most Two Factor Authentication security mechanisms use a mobile phone for this. The vulnerability of SS7 is almost new and this vulnerability was reported in August 2015, it is interesting to know that this vulnerability exists in the telecommunication infrastructure that is used by more than 800 communication companies in the world.
How does the SS7 flaw or vulnerability work?
The working mechanism of this security flaw is not so complicated, the hacker sends all phone calls made to the target phone to a single device.
The online audio recording system routes and then re-routes the desired call to the mobile phone user and thus performs a kind of Man In The Middle or MITM attack.

If hacked in this way, the hacker can identify the smallest movement of the user and use other hacking tools at his disposal to spy on all the user’s activities. It is interesting to know that Nohel has announced that this security vulnerability existed in information systems and that the spy and security services of the world knew about such vulnerability and sometimes used it.
SPY24: Various methods of hacking the phone without having a contact number and physical access
Hacking the phone with the victim’s IP and through Internet protocol communication
One of the most difficult methods of hacking a phone, which ordinary hackers are unable to do, is the hacking method directly without using a special program. Hackers who use this method have very high programming knowledge, they connect to the victim’s mobile phone in the network and then hack it using the operating system Kali Linux or Bactrak Linux.
Since these hackers have high knowledge in this field, they know which parts of the victim’s mobile phone are vulnerable and use those parts to penetrate the device. In order to become a professional hacker and be able to hack the number of the person you want, the first step is to learn the computer and the network Operating systems.
By using the MAC address and other useful information of the victim, this can be achieved by writing scripts or various exploits.
Hacking the phone using different software
There is various software for hacking the phone, of course, most of them must be installed on the target phone, but some of them provide you with the possibility of hacking the phone either through the phone number or by sending a link to the target.
In the following, we will introduce some of the most famous hacking software in the world and teach you how to work with them. In the previous episodes and other articles of SPY24 in connection with hacking through smashing and phishing, We mentioned hacking through malware and ransomware. in the following, we will discuss the introduction of famous applications in this field.
Hacking Android phones Android RAT
In fact, Android RAT is a very dangerous spy tool for hacking Android phones, RAT is a type of remote Trojan virus that looks like a completely normal Android program, which, like other Android software, is easily installed on The victim’s phone and is installed, but in its interior, it hacks all the information of the target phone remotely.
Of course, we must mention that many fraudulent and opportunistic sites introduce phone hacking programs that have a completely normal function and are called other people’s phone hacking programs and have no practical use. But the program that we introduce to you is completely real and practical, and we strongly recommend that you never use the program introduced in this article with the purpose of abusing others and respecting the rights of other people.
SIM card access:
As almost everyone now owns a mobile phone or smartphone and carries it with them at all times, mobile devices are increasingly used to verify personal identity, especially through online services. For this, a one-time password is sent to the user’s mobile phone via SMS or voicemail. They must then enter the code into a website or app for authentication, possibly as part of multi-factor authentication (MFA) or to recover an account.
It is a user-friendly and apparently safe method. But the fact that most users have linked their mobile phone numbers to bank accounts, email, and social networks also attracts attackers. If they get access to another person’s mobile phone number by changing the SIM card, they can use it for various criminal purposes. In this way, the attacker forwards all text messages and calls or can send himself a text message or – for example – call a paid service abroad.
It can also usurp (almost) an entire online presence by hacking into accounts that allow for cell-based authentication (like Twitter) or password recovery — including Gmail, Facebook, or Instagram, for example. Prominent victims include former Twitter founder and CEO Jack Dorsey and actress Jessica Alba: their Twitter accounts were hacked via SIM card swaps to then post objectionable posts on the platform.
It becomes expensive when the victim uses the (overly) popular mTAN or smsTAN method to release online remittances, i.e. the bank sends the transaction number to the customer via SMS. If the hacker also has access to data for online banking, they can empty their victim’s account from the comfort of their own home. A report by Bayern’s central cybercrime office shows that this method is being used not only across the pond but in Germany as well. In mid-2019, they arrested three criminals who used SIM card swapping to access at least 27 foreign bank accounts and make remittances.
Dendroid software
The dendroid program is an Android root program. Root programs are generally programs that change the source of mysterious software However, Android apps, such as games and other applications, have turned them into Trojans so that they can spy on the victim’s phone. Android is one of the most professional Android hacking programs that most hackers use to gain influence.
Are you looking to monitor the phone of your children or your girlfriend, boyfriend, and wife? Learn more about the best application in the world, SPY24 (link).
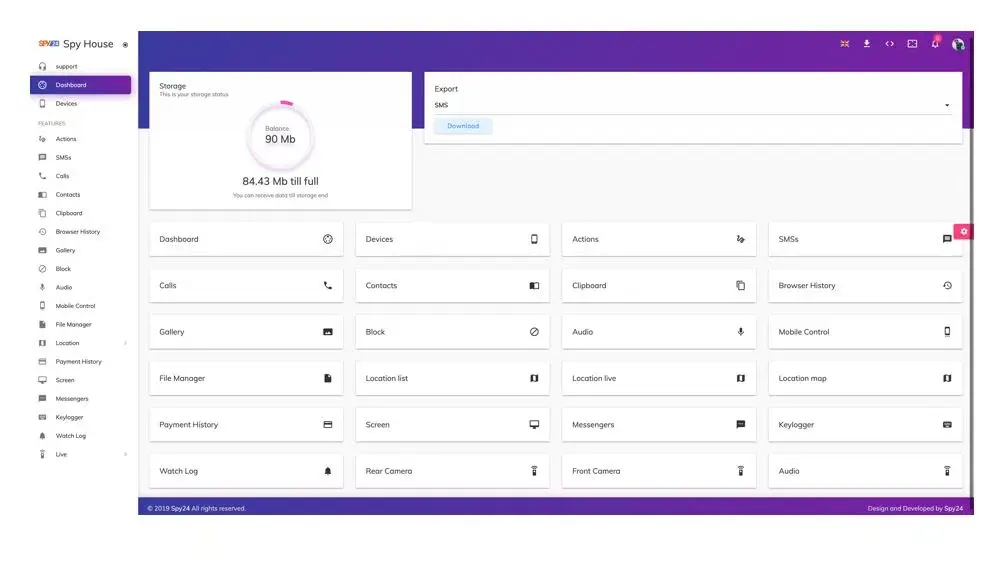
SPY24 Install application free The Most Powerful Hidden Spying App to Monitor Android, IOS Cell Phone & Tablet Device Remotely. Best Android Parental Control App for Kids & Teens Online Safety.
Now take the liberty to monitor Android, and IOS devices with exclusive features better than ever before Monitor all Voice & Text Messages Communication records, Listen to & Watch Surroundings in Real-time Unleash Digital Parenting with Android, IOS Spy App Spy (Surround Listing & Front/Back Camera Bugging) IM’s VoIP call recording on Android OS 13 & above With 250+ Surveillance Tools at your fingertips using Android Tracking & Parental Monitoring Software.
Conclusion :
In this article from SPY24, we first checked whether it would be possible to hack a phone without having access to the contact number or not. Then we checked different ways of hacking and accessing and listening to a phone without accessing the number.
We unveiled methods and protocols that allow hackers to easily hack mobile phones.
Then we came to understand how to access the location of the opposite person, for example, our child, through the phone.
Below are all the common questions in this field.
FAQs
Is it possible to hack a mobile phone without having a mobile number?
Hacking a mobile phone is a nightmare for many people, and unfortunately, hacking a phone through a phone number is also possible in today’s world. It must have happened to you to look at your phone for a moment and say to yourself, “Is my phone hacked?” In SPY24, we will fully address this issue.
How to hack someone’s phone information only through a mobile number?
Through a lot of programming knowledge, as well as familiarity with troubleshooting and network penetration, it is possible to penetrate the victim’s phone in various ways, such as the Kali Linux operating system or Termux in Android or Android-Rot operating system.
How to hack someone’s phone number without access?
For this, you must have access to the right tools, as well as a lot of knowledge, as well as enough information about the victim’s operating system, if you are a beginner, we suggest you follow SPY24’s articles.
What are the best applications for hacking mobile phones and listening to children’s conversations?
Many applications have been designed and marketed in the world, but you cannot use any application for this purpose. Because this can have many consequences, including information theft. Bank numbers and digital currency amounts, etc. should be from your children’s phones. So before doing this, collect complete and comprehensive information.
What is the best application for listening to conversations without having physical access to the phone?
SPY24 is one of the best applications in this field with many features, including the ability to access all conversations, recorded conversations, images, and personal information on social networks, as well as reasonable prices in different plans.