Are you worried about SS7 attacks and what they mean for your security? Signalling System 7 (SS7) is a type of telecommunications protocol used by telephone networks all over the world. It’s become increasingly popular with hackers, as it gives them unfettered access to phone numbers, text messages, location data, and more. In this blog post, we’ll look at what SS7 attacks are, how they work, and some steps you can take to protect yourself and your information.
An SS7 attack occurs when a malicious actor uses the SS7 protocol to gain access to a target’s private data. This type of attack takes advantage of vulnerabilities in the SS7 protocol, which allows them to intercept calls, read text messages, and access location data without the target’s knowledge. This can be used to obtain confidential information like credit card numbers, and bank account information, or even just to spy on someone.
For many people, the prospect of an SS7 attack may seem intimidating or even impossible – but it’s not. With the right tools and knowledge, anyone can perform an SS7 attack. This blog post will provide an overview of what SS7 attacks are, how they work, and how to protect yourself from them. We’ll also provide a few tips to help you stay safe and secure online.
What Is SS7?
There are a number of telecommunication standards, but Signaling System 7 (SS7) is one of the most important because it defines the way in which the network elements in a public switched telephone network (PSTN) exchange information and control signals in a standardized way.
This is because nodes in the SS7 network, also known as signaling points, are responsible for routing calls, text messages, and other services. Furthermore, advanced features such as call forwarding, caller ID, and toll-free numbers can also be implemented using SS7 infrastructures.
A telephone call routing and billing system is a part of this system, and it also provides advanced features such as Short Message Service (SMS) and advanced calling features. This signaling system may also be called Signalling System No. 7, Signaling System No. 7, or — in the United States — Common Channel Signaling System 7, or CCSS7.
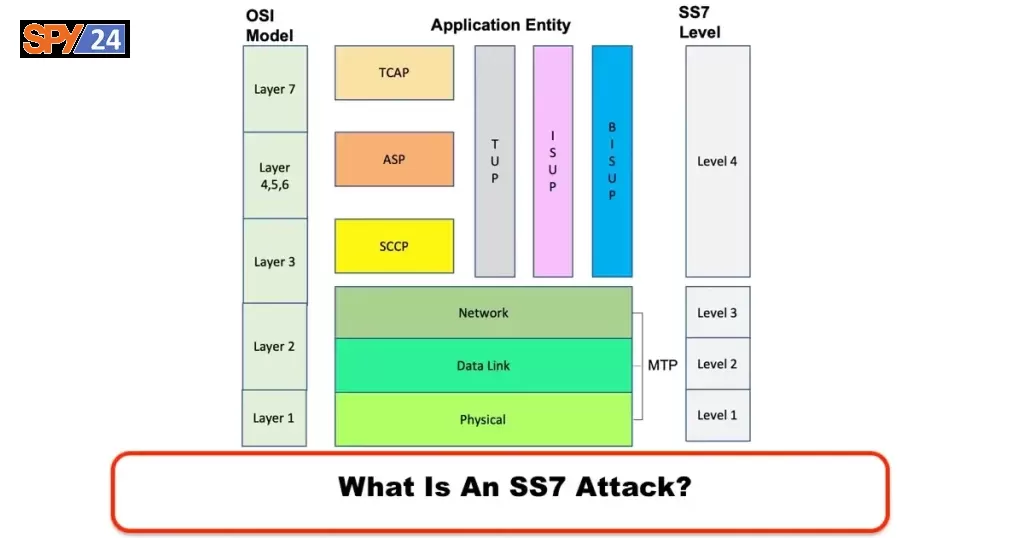
SS7 is a set of telephony signaling protocols that are used to set up, manage and tear down calls in the public switched telephone network (PSTN). It is also used in mobile networks for SMS, roaming, location services, and call forwarding.
As well as setting up, managing, and terminating calls, SS7 is the protocol that mobile operators use to manage SMS messages, location services, and call forwarding. It is a very powerful protocol, and it is also used by telecom operators to manage location services, and call forwarding. For more than two decades, telecom operators have been using SS7 as the standard protocol.
How Does SS7 Work?
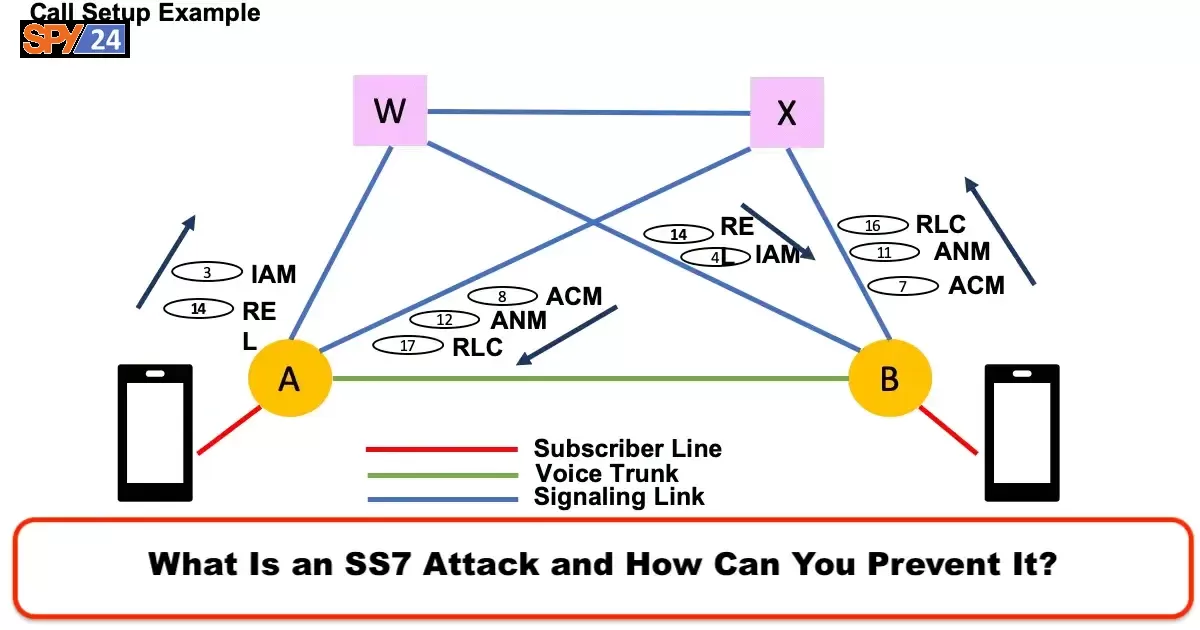
This protocol is responsible for initiating and terminating telephone calls across a digital signaling network to facilitate cellular and wired wireless connectivity. Most international public telephone calls are made through the public switched telephone network, which is a digital signaling network.
This protocol, known as the Signaling System No. 7 (SS7), manages the communication between two devices, such as a caller and a receiver, by transmitting messages that include requests for service, address information, and authentication information. It establishes a connection between the two phones and allows them to communicate.
In addition, to call waiting, SMS, prepaid billing, number translation, call forwarding, local number portability, and conference calling, there were other applications gradually incorporated into SS7, which allowed new solutions to be offered to the mass market, such as call waiting, SMS, prepaid billing, number translation, call forwarding, and conferencing.
These applications enabled telecom carriers to provide new services that were not previously available, such as the ability to access voicemail from any phone, block unwanted calls and texts, and easily transfer phone numbers from one carrier to another. These applications made use of advanced technologies such as Voice over IP (VoIP) and Session Initiation Protocol (SIP) to enable these services. They also allowed for the integration of cloud services and web-based interfaces to make these services more accessible and easier to manage.
What is an SS7 attack?
An SS7 attack is a form of a mobile cyberattack that exploits security flaws in the SS7 protocol in order to compromise and intercept voice or SMS communications over cellular networks. This type of attack primarily targets mobile phone communications and not WiFi broadcasts, similar to a Man-in-the-Middle attack or contact spoofing attack.
Because the SS7 protocol was designed to facilitate communication between telecommunication networks, it allows attackers to monitor the traffic of a given phone number and gain access to conversations, SMS messages, and authentication codes. This type of attack is especially dangerous because it is difficult to detect and can be used to intercept data without the victim’s knowledge. As a result, hackers have an opportunity to exploit the SS7 protocol for malicious purposes, making it a major security threat for mobile users.
How does an SS7 attack work?
By utilizing SS7 attacks, hackers are able to snoop on voice, text, and video communications using communication systems that are built on top of it. For SS7 strikes, a hacking group would only need a Linux system and the free SS7 SDK that can be downloaded online.
Hackers can target customers while deceiving the network into believing their device is an MSC/VLR by connecting to an SS7 system. Since SS7 was designed to be the universal language of telecommunications networks, it can be used to manipulate data.
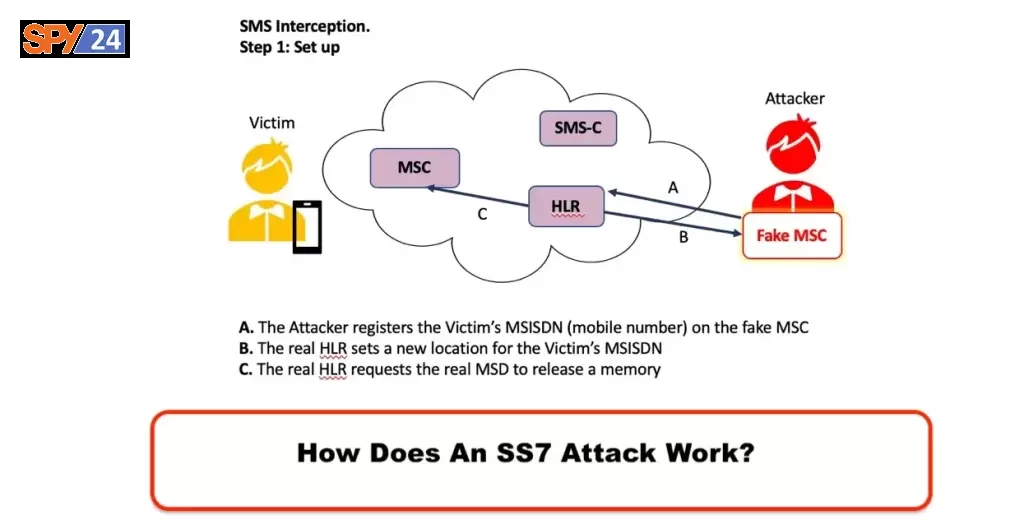
By exploiting weaknesses in the SS7 system, hackers can gain access to a user’s text messages, voice calls, and video calls on the same network. This type of attack is easy to carry out because the hacker only needs a Linux system and a free SS7 SDK to do it. SS7 does not have any security protocols in place, which means that the SS7 system is vulnerable to attacks.
Additionally, because the SS7 system is so widely used, any attack on the system can have a global impact. This makes SS7 exploitation a serious security threat to users around the world.
Consequences of the SS7 vulnerability
Hackers can obtain high-quality information from SS7 attacks due to the embedded monitoring elements. By exploiting the SS7 protocol, hackers can access a wealth of information, such as the location of mobile devices, call details, and SMS messages. They can also use this information to launch other attacks, such as phishing and malware.
By adopting best practices such as virtual private networks, encryption, and security awareness training, businesses can mitigate potential exposure. However, this capability makes it easy for network operators, governments, cybercriminals, and entertainment to track and compromise smartphones. In today’s digital world, nearly every device is capable of accessing the internet and transmitting data, making it vulnerable to malicious actors. To reduce the risk of their data being compromised, businesses should take steps to protect their data with measures such as encrypted connections, secure wireless networks, and employee education.
The telecom industry remained slow to implement safeguards for SS7 despite knowing its problems, and some failed to do so altogether. By adding new security protocols, 4G and 5G telecommunication networks have reduced the risk, but they must interact with older technologies. This means that older networks are still vulnerable, as they are still susceptible to the same SS7 exploits and there is no way to upgrade the older systems to support the new security protocols.
In its 2021 mobile phone report, the GSMA estimates that 30% of mobile connections are using 2G or 3G networks. It is clear that 5G adoption is on the rise, but as long as 2G and 3G networks are active, SS7 attacks will remain a concern. This is because SS7 attacks rely on exploiting vulnerabilities in the 2G and 3G network systems. As long as these networks are still active, attackers will be able to exploit these vulnerabilities and launch SS7 attacks.
How Does SS7 Attack Benefits Cyber Criminals?
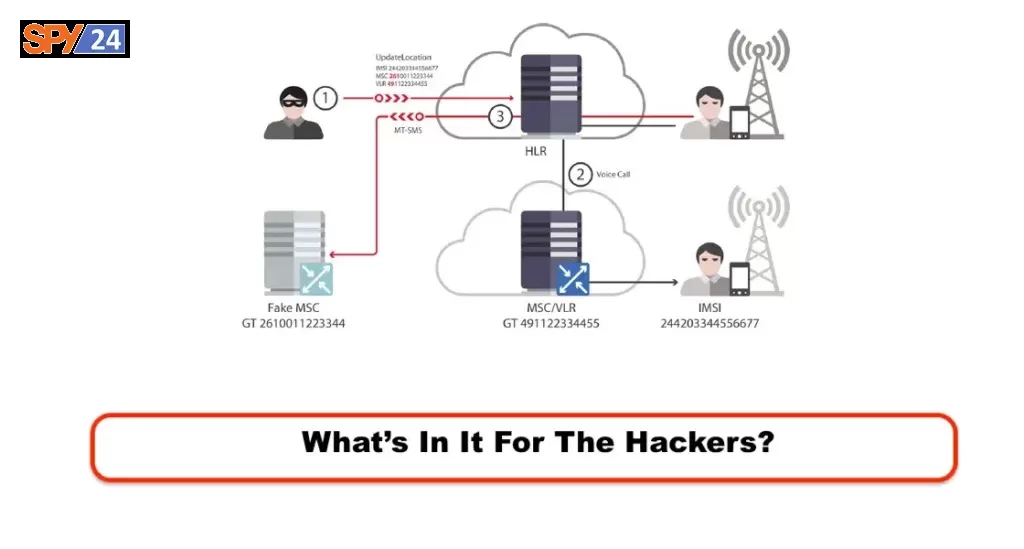
An attacker can access the same kinds and quantities of data as security agencies when they successfully use MiTM spoofing. Text messages, phone calls, and locations can provide hackers with valuable information. Man-in-the-Middle (MiTM) attacks involve intercepting and manipulating communications between two parties. By spoofing the communication, the hacker can gain access to the same kinds and quantities of data that the security agencies have access to. This allows them to gain access to sensitive information such as text messages, phone calls, and locations.
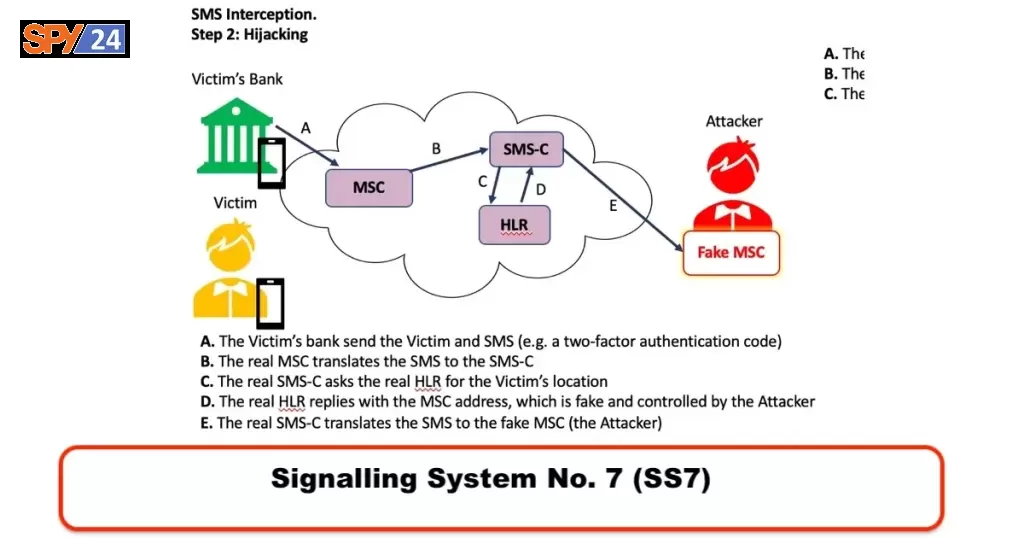
The SS7 attack is one of the most widely used security measures. 2FA (two-factor authentication) over SMS using SS7 cannot be secured because these SMS communications are not encrypted and can be easily obtained by hackers. With the passcode from the SMS, a malicious user could change your password for WhatsApp, Google, Social Media, and even your bank account.
SS7 is a set of signals used by mobile operators to communicate with each other. These signals can be used by hackers to gain access to the user’s mobile phone. Once they have access to the phone, they can intercept the SMS messages sent for two-factor authentication and use them to gain access to the user’s accounts. Therefore, it is essential to protect your phone from SS7 hacking, as it could lead to the compromise of all your accounts.
How Do Attackers Carry Out an SS7 Attack?
SS7 vulnerabilities can be exploited in the following ways:
SS7 attacks require you to establish a connection with the SS7 network and launch an application to fool your intended subscriber into thinking a code is roaming MSCs or VLRs in a network.
Get SS7 Connection
- In order to get an SS7 connection, you will need an international point code and a Global Title. SS7 connections may also use local point codes depending on the vendor. The new network code will allow them to have a variety of international titles, IMSIs, and MSISDNs if they are a mobile operator. If you do not want to purchase a global title directly from the phone company, you can get one from a phone company.
- Your GT can be broadcast across all networks through an SS7 aggregator you link to. Accordingly, your GT traffic will be diverted by the aggregator along the route taken by your application or node. A global mobile phone network is typically linked by an aggregator broadcasting GT bands from MVNOs.
- As each telecom carrier is responsible for modifying the routing of your GT to the hosting node, you will need to establish direct contact with them. Each phone company must be enrolled separately, therefore.
Use SS7 Toolkit
Creating your own SS7 app or purchasing an existing one is the next step after you connect to the SS7 system. The SDK must have the SS7 libraries and stacks you need in order to build the SS7 hacking software.
Register SS7 App as a Real Phone
A phone must first enroll in the app before joining a roaming network. In order to verify the mobile number, you will need the IMSI from the sim card. A mobile number can be obtained quickly, but IMSI information can be difficult to acquire. Obtaining the IMSI information of the person’s mobile phone number requires the use of the IMSI catcher tool. After receiving the SRI-SM and contact information from the HLR, the HLR responds by sending the IMSI and roaming data.
Roaming details include the area code and country code. After constructing the status update together with other variables, the SS7 hacking app launches a TCAP discussion with the SS7 node based on the IMSI information.
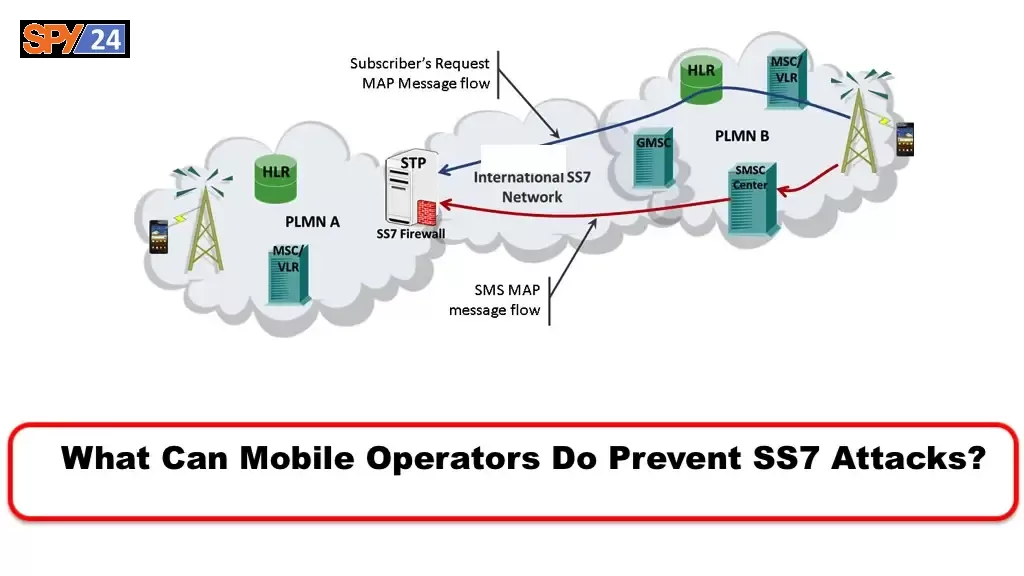
There must be an address for the SCCP calling party and a number for the calling party. An IMSI is used to generate the calling party address, and the GT is used to generate the calling party address. If the HLR replies with Insert Subscriber Data during Update Location, the subscriber data will be added to the HLR. The application software must recognize the ISD to the HLR in order for the update location method to work and for the app to attach as a smartphone. The enrollment process is completed when the HLR transmits an updated location acknowledgment.
In this case, hackers will be able to interfere with your calls, texts, WhatsApp, Facebook, and other apps via an SS7 attack.
How to Prevent SS7 Attack?
Small businesses, consumers, and organizations are not aware of the vulnerabilities and risks associated with the SS7 system. Due to this, it is difficult to correct or remove the flaws in SS7.
A GSMA report recommends prioritizing education and awareness when operating mobile networks. The increased consumer focus on security controls will lead to customers securing their phones and IoT devices. This is especially true when it comes to essential services and programs such as Smart Homes and Smart Offices.
In the event of an SS7 attack, you have no choice but to shut off your gadget, but you already know this isn’t a wise choice. The following steps should be taken:
Multi-Factor Authentication
SMS-based two-factor authentication is not secure, yet it’s widely used. Users are increasingly turning away from SMS-based user authentication in favor of alternatives that don’t rely on dated standards like SS7. The likelihood of an SS7 attack can be reduced by more than 90% when several different authentication techniques are combined.
Surveillance & Event Analysis
It is imperative that businesses are able to monitor what is happening when an SS7 system is successfully breached. Keeping them informed about security incidents affecting both corporate systems and devices is essential. Including this in a mobile security plan for a company is a must. As a result, companies need to implement a defensive strategy that identifies risks and reacts before they lead to harm.
Recurrent Updates
The process of protecting information is not one-time, even when it is automated. Increasingly sophisticated cybercriminals develop new vulnerabilities and methods for infiltrating systems and stealing sensitive data. It is essential to manage patches efficiently in order to enhance adaptive defense. Businesses can patch known security flaws via firmware and software updates by using real-time endpoint protection analysis.
Be Aware
Understanding your attacker and potential attacks is the first step toward neutralizing them. In order to prevent hostile actions such as SS7 attacks, it is important to know how frequently they occur.
In spite of this, it is unlikely that hackers will target you for monitoring due to the sheer number of people using mobile phones. You have a far greater chance of getting hacked if you are a CEO, a doctor, a lawyer, or someone with critical private data on your mobile device. It is possible to get hacked if you still use SMS-based two-factor authentication.
As easy as it is to carry out SS7 attacks, and considering the damage they may cause to both the target and their phone company, it can only be hoped that advancements in telecom will shield us, the end users. You can protect against SIM swap attacks, SS7 attacks, eavesdropping, and location tracking with Efani because it prevents SIM swap attacks and other security flaws.
Why is SS7 still a security threat?
Even though the old signaling protocol is supposed to be controlled, SS7 still has a lot of security holes. In 2017, hackers exploited SS7 through phishing and spamming attacks to drain money from German online bank accounts. In addition to routing and eavesdropping, SS7 can also be used for eavesdropping.
It is extremely important for voice and SMS communications to use the SS7 protocol for exchanging information. The protocol is vulnerable to security vulnerabilities, which have the potential to enable larger, more targeted attacks. Several classified US Justice Department disclosures reviewed by The Washington Post alleged that controversial surveillance firm NSO Group offered “bags of cash” to gain access to cellphone networks around the world.
A number of purposes can be achieved through the SS7 network, including tracking, gathering intelligence, intercepting communications, and perpetrating fraud. Groups of criminals, enemies of the nation, and surveillance companies are among the attackers.

It was very difficult to stop some of these attacks. AdaptiveMobile Security CTO Cathal McDaid says spyware vendors always seek access to SS7 networks. In the future, HTTPS 5G networks will also be accessible to adversarial actors by mobile operators, including surveillance companies.
SS7-based attacks are a major concern, but network security measures are always taken to prevent them. Russian and Belarusian subscribers were barred from accessing Kyivstar, Vodafone, and Lifecell networks in an SS7 security measure taken by Ukrainian operators.
Conclusion
The SS7 attack is a type of security threat that can be used to access private information from smartphones. In this article, we discussed what an SS7 attack is and how it works, the risks associated with it, and some tips for protecting yourself against it. It’s important to remain vigilant when it comes to your personal data and take the necessary steps to protect your information.
An SS7 attack takes advantage of a vulnerability in the global network that connects mobile carriers. It allows hackers to intercept text messages, track phone locations, and even listen to phone calls. To protect yourself, it’s important to use two-factor authentication, secure your accounts with strong passwords, and use encryption when possible.
So if you are looking to stay up-to-date on cybersecurity tips and tricks, follow our blog posts. Thanks for taking the time to read this article. If you have any questions or concerns about SS7 attacks, please leave them in the comments section below and we will be happy to help.
SPY24 Install application free The Most Powerful Hidden Spying App to Monitor Android, IOS Cell Phone & Tablet Device Remotely. Best Android Parental Control App for Kids & Teens Online Safety.
Now take the liberty to monitor Android, and IOS devices with exclusive features better than ever before Monitor all Voice & Text Messages Communication records, Listen to & Watch Surroundings in Real-time Unleash Digital Parenting with Android, IOS Spy App Spy (Surround Listing & Front/Back Camera Bugging) IM’s VoIP call recording on Android OS 13 & above With 250+ Surveillance Tools at your fingertips using Android Tracking & Parental Monitoring Software.