How to Hack Email Accounts: A Beginners Guide

One of the most well-known email service providers is the Google platform. Every day, millions of people visit their accounts globally. Despite its greatest efforts to shield users from hacking, Gmail is often a target for those with malicious intent, which is mainly due to its popularity.
As a result, many users of Google accounts make it simpler for hackers to access their data. When account holders install dubious applications or access private information on public networks, hackers have a way in.
There are several ways to break into Gmail accounts and hack email. Hackers may make use of trojan horses, phishing, keylogging, web browsers, and surveillance software. Here in this article, we answer the question of “how to hack email accounts.”
Keylogging
The keystrokes that a user presses on the keyboard of a computer or mobile device may be recorded by a number of different programs. These applications run in the background and often get access to their data via the shared memory of the mobile device.
The fact that the programs may be used in stealth mode while the user is not aware of their presence makes them an excellent choice for hackers.
While there are other acceptable reasons to use a keylogger, such as keeping track of your child’s Internet use, hackers often prefer this approach. Other justifiable reasons to use a keylogger include attempts to keep a careful eye on your children and employees while using the Internet.
The application known as SPY24 is the best tool if you want to hack email it has a lot of popularity and is used by hackers of varying degrees of experience. This program runs in the background, the installation scarcely takes any time at all, and it offers reports that are updated with new information on a range of topics every five minutes.
SPY24 features a keylogger that helps you hack email. In addition to this, this handy software makes it possible for you to read all of the emails that have been sent back and forth, as well as the timestamps and contact information associated with each communication.
SPY24 has the capability to get information on the sender of an email and to block them. Since it is hidden and works in the background, the target won’t be able to see it when it operates.
Using SPY24 to Hack Google Accounts: A Step-by-Step Guide
Visit www.SPY24.pro. Enter your email address. Choose the one that best suits your needs. You will get an email with your login details. Choose the kind of device you are using. Choose the item that needs to be watched. Either an iOS or an Android smartphone may be spied on by the target. You also have the option to select after that if you are willing to. Install the SPY24 tracker onto the target device.
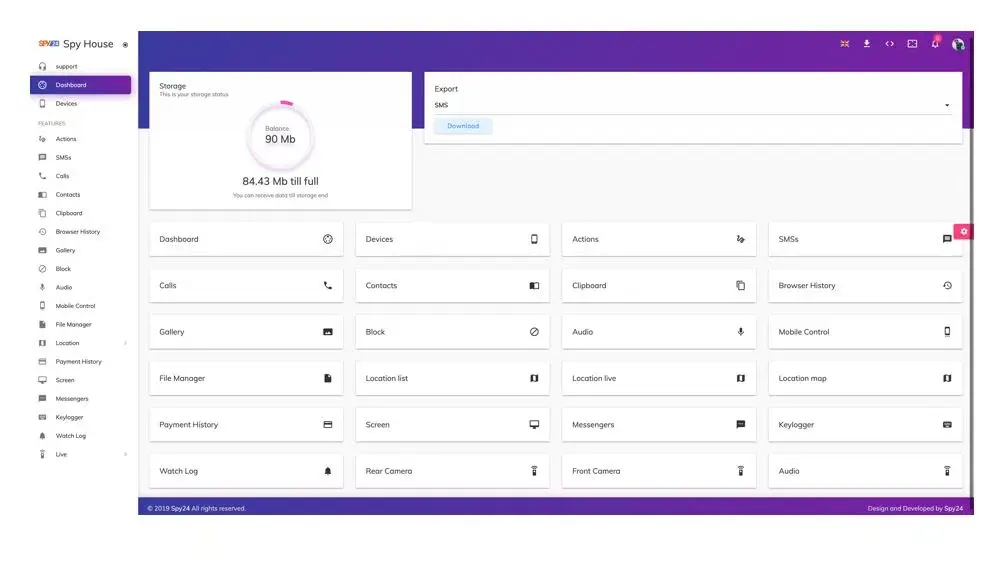
You won’t need to have physical access to the phone again until the very beginning of the setup process. To turn on the device, follow the instructions that appear on the screen. You should check your email after logging into your online SPY24 account.
SPY24 Install application free The Most Powerful Hidden Spying App to Monitor Android, IOS Cell Phone & Tablet Device Remotely. Best Android Parental Control App for Kids & Teens Online Safety.
Now take the liberty to monitor Android, and IOS devices with exclusive features better than ever before Monitor all Voice & Text Messages Communication records, Listen to & Watch Surroundings in Real-time Unleash Digital Parenting with Android, IOS Spy App Spy (Surround Listing & Front/Back Camera Bugging) IM’s VoIP call recording on Android OS 13 & above With 250+ Surveillance Tools at your fingertips using Android Tracking & Parental Monitoring Software.
Phishing
In comparison to keylogging, using this method to hack email accounts is far more difficult. Phishing is the practice of deceiving users into providing personal information by tricking them into visiting fake websites that seem just like genuine ones.
Phishers, when using this method of hacking via social engineering, would generally develop phony login sites that are designed to seem like those used by Gmail, Yahoo, or other email service providers. If you try to input your login credentials on one of the false login sites, cybercriminals will immediately be able to take the information from your computer.

Phishers, on the other hand, can send an email that looks very much like one that Google or Yahoo would ordinarily send. Often, these emails will include links to phony login sites, which will then ask you to change the password for your email account or update your account details.
It is also possible to construct an online identity of someone you know and use it to trick you into supplying your email login credentials. This is referred to as “hoodwinking.” A significant amount of hacking expertise along with previous familiarity with HTML, and scripting languages such as PHP/JSP, and CSS is required for one to properly conduct a phishing attack.
Phishing is generally regarded as a criminal act and is thus illegal in most areas. We regret to inform you that turning on two-factor authentication for your email accounts will not be of any assistance. Because of this, you need to exercise extreme caution before disclosing your email login credentials to anybody.
Before sharing any of your personal information, you should verify the domain name from which the email originated. Ignore any emails that seem to be from a questionable source and prompt you to change your password if you haven’t specifically requested this action.
Using the browser’s built-in password manager to hack emails
If you want to get into someone’s Gmail account using this technique, you will need physical access to the target device, which may be a personal computer, a mobile phone, or a tablet.
It is possible that it will be difficult to remember all of the login information for each account given the large number of distinct accounts to which everyone has access. As a direct consequence of this, a sizeable percentage of users will consent to allow their browsers to store and manage their passwords.
You are, however, making it easy for others to access your accounts by doing so. This might be a problem. Launching the website or the application, followed by logging in, is required of the person in question for as long as they have possession of the device.
Hackers may get access to the actual password information by utilizing the browser’s password manager, and once they have this information, they can use it to log in to other websites. In order for them to do this, they will need to:
- Launch your preferred web browser like Google Chrome. Choose “settings” from the menu.
- Have access to the browser’s settings as well as the password manager by clicking the three dots that are located in the upper right corner. Make sure that the “Autofill” option is selected in the menu on the left.
- Go to the right side of the page and choose the “Passwords” option to change your password. Find the Gmail account you want to see the password for, then choose the eye symbol from the toolbar.
Password Guessing and Resetting
Email hackers also make advantage of this strategy, which is known as social engineering. If you are interested in learning how to hack email accounts, you should not be concerned with the process of password guessing or resetting.
It is far simpler to utilize this method to access the mailboxes of those you already know as opposed to those who are totally strangers. In order to get access to the target person’s information, the technique entails exerting influence on the target person’s thinking.
It is necessary to have a high level of familiarity with the person whose password you are trying to guess or reset since these activities demand a high level of critical thinking and social competence. Hackers that use this method are often members of the victim’s immediate family, circle of acquaintances, or place of employment.
These people know a lot about you, including the things you like doing in your spare time, your birth date, and other personal information. As a result, it is simpler for them to figure out the password to your email account, and in particular, the security question.
What Hackers Can Do with Just Your Email Address
Here in this part of hacking email accounts, we look at the things that a hacker can do by getting access to email contents. When hackers gain access to your email, they have access to a significant amount of information about you. The following is a list of the capabilities that they possess:

They Can Impersonate You
It is commonly known that you should never trust an email that does not seem to have been sent by someone you know and respect. Emails that falsely say you have won $1 million in a lottery that you did not participate in can any longer readily deceive people as effectively as they once could.
But con artists are coming up with new strategies to get past this. The piece of advice teaches us to be more skeptical of emails that come from unknown senders, but it also teaches us to be more trusting of emails that come from friends and family members.
Scammers take advantage of this vulnerability by breaking into email accounts and utilizing those accounts to communicate with the victim’s friends and relatives. If the con artist is skilled at imitating others, they may convince the victim’s connections that they are speaking with the victim, while in reality, they are talking to the con artist.
At this stage, the con artist is free to urge the victim to carry out any action that they choose. They can tell their pals that they are experiencing some kind of financial difficulty and urge them to send some money to the hacker. They may email a link to a dangerous application and say it’s a video of the buddy doing something humiliating, but in reality, it’s a video of the infected program.
In light of this, you need to proceed with extreme care, even if the email seems to come from a trusted friend of yours. If you have any concerns about the legitimacy of their request, you should make an effort to get in touch with them over the phone or via another channel, such as social media.
Sending phishing emails
A cybercriminal’s plan might begin with the simple act of obtaining your email address as the first step. If someone has your email address, they have the ability to get in touch with you and make an attempt to learn any personal passwords that are tied to that account. They will be allowed access to your accounts as soon as they are in possession of the corresponding pieces of personal information.
Phishing emails are one of the most prevalent methods used by hackers to collect user credentials. Hackers use a variety of other strategies as well. The message will pose as a trustworthy email coming from a reputable source in an effort to deceive you into providing your personal login information and passwords so that the sender may steal your identity.
When you click on the links in the email, you will be led to a website that looks almost exactly like the real one you were trying to access. As a result, you may not even realize that you have been tricked. Sites that are designed to seem like eBay and Amazon are rather widespread, as are business portals and login sites for Microsoft.
As you submit your information into the forms, the thieves capture it and use it to get access to your personal accounts using your email address and password.
Hackers may also contact you through email with a warning message that your account has been accessed without authorization. This is another tactic they may utilize. The request will require you to generate a new password, and as soon as you do so, the hacker will have access to your account as well as the password you generated.
Spoofing your email address
Email spoofing occurs when a con artist uses code to change the header of an email so that it seems to have originated from a valid domain, even though the email did not originate from that domain. The word “spoofing” is occasionally also used to describe look-alike emails that are meant to fool the receiver, such as [email protected].
This use of the phrase occurs less often than the other uses of the term. There is a possibility that when you received an email and did not consciously verify the form address, your brain auto-corrected the “r” and “n” into an “m.” If you checked the address, you would have seen the error. And that is precisely what the con artist intends to achieve.
The Unicode inspector is a useful tool for spotting foreign characters that seem to be lookalikes as well as other forms of deception. Another illustration: you check your email and see a message from your friend at [email protected].
Currently, email providers display email addresses in lowercase, but it’s doubtful that our brain would be suspicious of a name that’s capitalized. Nevertheless, when the email is pasted into the Unicode inspector, it indicates that the character in question is a lowercase “L,” not an “i.”
Finding personal information
If the hacker manages to hack an email account used for business, the consequences might be catastrophic for the firm. The hacker has access to any critical financial data, login credentials for the firm, or passwords to physical locks. They might commit either digital or physical theft against the company using the information they have obtained.
There is a possibility that personal accounts’ inboxes include private information that is hidden from view. Any interaction with your bank might potentially give away information that a con artist could use to make transactions on your behalf.
If your account does not include any significant company data, a hacker will likely settle with stealing your identity rather than accessing your account.
Hackers might get a lot of information from your emails if they have access to them. Your name and address will be shown prominently on any invoices, and the con artist will be able to access any images you may have sent to them. If the hacker obtains sufficient information about you, they may use that information to steal your identity and sign up for services under your name.
Be sure that every piece of personal information you have stored online is protected from prying eyes at all times. It is important to educate yourself on the many pieces of information that may be used to steal your identity so that you are aware of what information you should keep private and what information you can disclose.
Sending emails to your contacts
After breaking into your account or even just getting their hands on your email address, the most apparent thing a cybercriminal can do is send emails from your account.
This may nevertheless lead to a lot of complications. A hacker who knows your email address and has access to an outbound mail server and mailing software may send fake messages even if they do not have access to your email account.
They are able to send out a number of schemes through email that you would prefer not to be linked with using your fake address. These schemes include messages with links to malware that is dangerous to your computer and demands money.
This might, at best, damage your reputation, and, at worst, lead to your unintentional participation in illegal activities that put others in danger. Either way, the consequences could be negative.
They May Find Out While You’re Not Home
If a hacker accesses your email and discovers transportation tickets or reservation information for a hotel, they will know that you are not at home on those particular days. When this information is combined with your address, which was obtained through an invoice, a con artist will know exactly when and where to commit a home invasion.
It is essential that you maintain your trip plans and destinations a secret; otherwise, you run the danger of inviting criminals into your property. Even tickets to an event may be programmed to indicate when you won’t be there.
Keep things as quiet as possible while you are gone since there are several ways that thieves may know when you are away on vacation. Don’t worry; you’ll have plenty of opportunities to post your beach selfies and pictures when you go back to your house.
They Can Bypass Two-Factor Authentication
A hacker may sometimes be in possession of the account password for another user, but they will be prevented from accessing the account by a two-factor authentication scheme that uses email. Hackers are able to bypass two-factor authentication systems by obtaining access to the locations where authentication codes are presented.
If a hacker were to obtain access to your email account, they would be able to bypass any email-based two-factor authentication methods that you had set up.
Some websites may contact you through email if they see an odd login pattern on your account. This email will inquire as to whether or not the login attempt was legitimate, and it will often include a button for you to click in order to validate the login attempt.
If hackers obtain your email address, they may circumvent this security barrier by permitting their login attempt whenever a new email arrives. This gives them access to your account.
Accessing your online accounts
When you sign up for a website that has questionable security procedures, the website will send you an email verifying both your username and password. This happens whenever you sign up for a new account with the website. All of this information will be plainly visible to anybody who has access to your email account.
Because of this, the majority of websites do not or are unable to divulge the password in the confirmation email after user registration. Yet, it is probable that your username will be included in the email that you get after signing up for these services. A hacker may use this information to obtain access to your account.
If you use the same password on your email account as you do for everything else, for instance, a hacker will already have the password they need to access your other accounts since you have used the same password on your email account.
In case you do not, the hacker will still be able to request a password reset from each site. Your account is then sent with a reset email from the website, which the hacker may use to alter the settings according to their whims.
Stealing financial information
If a hacker is able to obtain your financial data via your hacked account, such as the information related to your debit or credit card, the repercussions may be quite detrimental.
Hackers may use the information you provide to make purchases online, using up the money you have available in your account or, even worse, opening new accounts, running up credit, and applying for further loans and payment cards in your name. This might have a catastrophic impact on your personal credit score as well as a significant influence on the long-term ambitions you have.
Blackmailing
Another terrifying possibility that may shock you about what someone else may do with your email address and password is the following: “[Hackers] can use this access to spy on you and examine your most personal emails,” said Daniel Smith, director of security research at the cybersecurity firm Radware. “[Hackers] can use this access to review your most personal emails.”
If hackers get access to your email account and locate sensitive material in your inbox — the kind of stuff you probably wouldn’t want to make public — they may use that information to dox, blackmail, or even threaten you with legal actions.
For instance, your email inbox may include messages from a lover you’re hiding, and if those messages were ever made public, it would be disastrous for both your professional and personal life. Hackers are able to uncover papers that include your address and phone number, which are often used in Doxxing attacks such as inviting the police to a person’s house. This is an equally alarming situation.
Is it safe to give your email address out?
If you freely share your email address, there is a risk that it could find its way into the wrong hands. If this happens, you might find yourself inundated with obnoxious commercial emails or become a victim of a hacker who will use your email address to carry out a broad variety of damaging acts.

Why would a scammer want your email address?
- Gmail often stores sensitive personal information such as financial information, contacts, and secret work-related emails, which a hacker may exploit for identity theft or financial fraud if they get access to the account.
- If hackers gain access to your Gmail account, they might use it to send unwanted emails to your contacts.
- The hacker may use your Gmail account to impersonate you and do damage to your reputation by sending damaging messages to the people in your contact list. This is called “hijacking your online identity.”
- Gmail is often used as a recovery email address for other accounts, such as social networking or online shopping accounts. This allows users to regain access to their accounts if they forget their passwords. Your Gmail password might be used by the hacker to get access to any of these other accounts.
- By using a technique known as crypto-jacking, a hacker may mine bitcoin on your computer without your awareness.
What are the telltale signs that someone has gained unauthorized access to your email account?
If you are unsure whether or not someone has hacked into your email account, there are several warning indicators including the following:
Your password does not work anymore
If you are unable to enter your email account anymore, this is one of the most obvious signs that your account has been hacked. If you try to log in to your email account with your typical password, but you are unable to do so, it is quite probable that the password has been altered by another user.
When hackers have successfully acquired access to your email account, one of the first things they do is change the password so that you cannot sign in.
There are email messages in your account that you are not familiar with
Hackers, on the other hand, do not always change your password, and there are situations when you will still be able to access your email account. It’s possible that you’ll see messages in your sent folder that you don’t recognize since you didn’t send them.
This is because the messages were sent by someone else. Nevertheless, it’s possible that you have received emails from websites that you haven’t authorized requesting that you reset your password.
This might be because hackers have gained access to your email account and are attempting to use it to change your password on other websites. Texts that you aren’t familiar with are a red flag that a hacker may have gained access to your account.
Several of your friends have mentioned that you have sent them strange texts or spam
If the people you communicate with the claim that they have received spam from your email address, this is a warning sign that your email account may have been hacked and that your data may be in danger.
Your log has many IP addresses from different sources
Several email providers provide a feature that exposes your IP address. This means that your IP address is tracked each time you log in to your email account, even if you disable the tool.
With Gmail, for instance, if you scroll all the way to the bottom of the page, you will come across the phrase “Details” in the upper-right-hand corner of the screen.
If you click on this, you will be able to see the geographical locations associated with the various IP addresses that have logged into your account. If you never visit the account from a location other than your home or place of employment, the IP address will not change. If more than one person has logged into your email account, you will see that various IP addresses are shown.
What to do in case your email account has been compromised
After discovering a breach in your email account, you need to move fast to kick the hacker out of your account. Regaining control of your email and preventing future breaches of its security may be accomplished with the aid of the following email security recommendations:
Be sure to update your password
Start the process of password recovery for your email provider, and then create a new password that is both lengthy and different from any other. If you have used the password for your previous email account for other accounts, you need to change the password for each of those accounts as well, and make sure that the new passwords are all unique.
Modify your security questions
Change your security questions as soon as possible if your email service provider asks you questions like “what was your first school?” or “what was your mother’s maiden name?” If you have a habit of oversharing information online, it will be easy for hackers to uncover the answers to queries like these via your social media accounts.
Activate the two-factor authentication feature (2FA)
If your email service provider supports two-factor authentication, you should activate it as soon as possible. Two-factor authentication is safer than the traditional method of using a series of security questions that are simple to answer incorrectly. Include two-factor authentication as a fundamental part of your email security procedures.
Inform your various acquaintances
Notify your contacts that the security of your email account has been breached, and advise them to be vigilant for any strange emails that seem to have been sent by you. Make it clear to them that you were not the one who sent these messages and that they should remove them as soon as possible.
Make sure that your antivirus software is up to date
Ensure that any security software installed on your devices is running the latest available version by performing an update. Start defending yourself immediately with specialized Internet security solutions if you haven’t already done so before. Phishing emails and websites, as well as the spyware that email hackers like to use, may be avoided with AVG AntiVirus FREE’s protection.
Regain access to your accounts. By regaining access to your accounts and permanently booting the email hackers out of your system, you can protect yourself from further intrusions. Keep reading to learn how to restore access to your Gmail, Yahoo, and Microsoft email accounts once they have been compromised.
A guide to keeping your email address secure
Your email address may be protected against cybercriminals to a large extent by developing and maintaining sound cybersecurity practices. The followings are important considerations to bear in mind:
Use a unique password
Under no circumstances should the password to your email account be used on any other website. Individual passwords reduce the likelihood that an account may be hijacked in case the data of another website is compromised.
Make use of a randomly created password
Check that your password includes capital letters, lowercase letters, digits, and symbols. The more unpredictable and lengthier it is, the lower the likelihood that a hacker will be able to guess or break it. A password manager may assist you in generating a robust password, which it can then keep for you.
Activate the MFA
Multiple-Factor Authentication (MFA) is supported by the majority of email service providers. When you log in using MFA, you are required to provide a second piece of information in addition to your password. The second piece of information (or component) may be anything like a randomly generated code, a scan of your face, or a swipe of one of your fingerprints. Because of the fact that hackers won’t have access to the second piece of information, MFA makes it far more difficult for them to break in.
Establish distinct email addresses
You should give some thought to using a different, “throwaway” email address for all of your online buying needs. It will not only keep your main email address free of the clutter of advertising emails, but it will also lessen the effect of any data breaches that may occur.
If your main email address is related to your financial accounts as well as any other sensitive accounts, it will be more difficult for hackers to find out those other accounts using your throwaway email address.
Conclusion
In this article, we answered the questions regarding how to hack email and how to protect it. Are you beginning to see any particular behavior in your online life? You may attempt to get ahead of the situation in a handful of different ways before it gets too terrible.
If you find out that your email address has been used to send spam emails, you should immediately reset your password. In addition to this, you should inform your contacts so that they are aware they should disregard anything coming from your account. We hope you find this article in SPY24 useful! You can also read our other articles such as How to Hack Gmail Accounts or Recover.
FAQs
Here are some of the Frequently Asked Questions about hacking email accounts:
Can responding to an email get you hacked?
Even though email viruses are still a concern, opening and responding to an infected email won’t result in downloading a virus as long as the email’s harmful link or attachment is not clicked.
What are hackers seeking?
Regrettably, some hackers only want to take your data to show off their skills. They are not driven by a desire for financial gain, unfettered access to resources, or the chance to steal the identities of your users. They only want to demonstrate to themselves—and maybe their hacker friends—that they are capable of getting past your protections.
Can someone hack my email address to break into my bank account?
It’s conceivable that hackers may use your email to access your credit card or bank account data, deplete an account’s assets, or pile up charges. They could even sign up for websites and services using your email and password, charging you a monthly fee as a result.